Ούτε ένα, ούτε δύο αλλά τέσσερα (4) exploits του TaiG “κλείνει” το iOS 8.1.3 το οποίο δόθηκε σε κυκλοφορία εχτές το απόγευμα από την Apple.
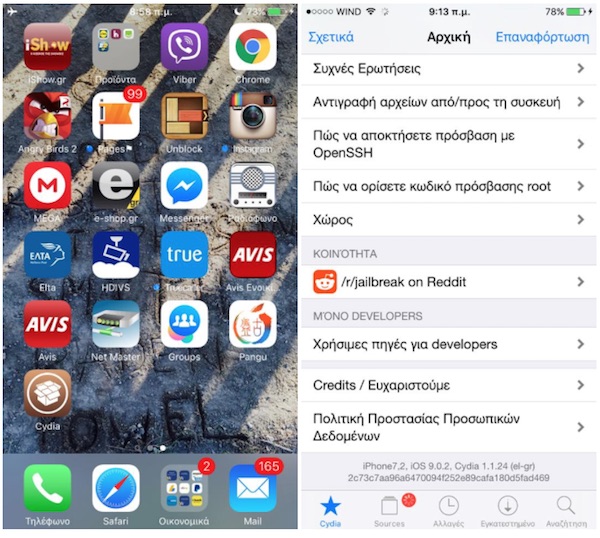
Οι χρήστες που έχουν ήδη Jailbroken συσκευή θα πρέπει να προσέξουν ώστε να μην προχωρήσουν σε αναβάθμιση του λειτουργικού της iOS συσκευής τους.
Πλέον αναμένουμε την επόμενη κίνηση από την πλευρά της ομάδας TaiG, η οποία στο πρόσφατο παρελθόν είχε δηλώσει απολύτως βέβαιη για την επιτυχία του Jailbreak tool στο επερχόμενο iOS 8.2.
Apple recently released iOS 8.2 beta 3. Are you confident your tool will be able to jailbreak this software?
Yes. Absolutely!
Ακολουθεί η λίστα με τα exploits που διορθώθηκαν στο iOS 8.1.3:
AppleFileConduit
● Available for: iPhone 4s and later, iPod touch (5th generation) and later, iPad 2 and later
● Impact: A maliciously crafted afc command may allow access to protected parts of the filesystem
● Description: A vulnerability existed in the symbolic linking mechanism of afc. This issue was addressed by adding additional path checks.
● CVE-2014-4480 : TaiG Jailbreak Team
dyld
● Available for: iPhone 4s and later, iPod touch (5th generation) and later, iPad 2 and later
● Impact: A local user may be able to execute unsigned code
● Description: A state management issue existed in the handling of Mach-O executable files with overlapping segments. This issue was addressed through improved validation of segment sizes.
● CVE-2014-4455 : TaiG Jailbreak Team
IOHIDFamily
● Available for: iPhone 4s and later, iPod touch (5th generation) and later, iPad 2 and later
● Impact: A malicious application may be able to execute arbitrary code with system privileges
● Description: A buffer overflow existed in IOHIDFamily. This issue was addressed through improved size validation.
● CVE-2014-4487 : TaiG Jailbreak Team
Kernel
● Available for: iPhone 4s and later, iPod touch (5th generation) and later, iPad 2 and later
● Impact: Maliciously crafted or compromised iOS applications may be able to determine addresses in the kernel
● Description: The mach_port_kobject kernel interface leaked kernel addresses and heap permutation value, which may aid in bypassing address space layout randomization protection. This was addressed by disabling the mach_port_kobject interface in production configurations.
● CVE-2014-4496 : TaiG Jailbreak Team
Επίσης, μία ακόμα ευπάθεια του Kernel διορθώθηκε στο iOS 8.1.3 και πιστώνεται στους @PanguTeam & Stefan Esser
Kernel
● Available for: iPhone 4s and later, iPod touch (5th generation) and later, iPad 2 and later
● Impact: Maliciously crafted or compromised iOS applications may be able to determine addresses in the kernel
● Description: An information disclosure issue existed in the handling of APIs related to kernel extensions. Responses containing an OSBundleMachOHeaders key may have included kernel addresses, which may aid in bypassing address space layout randomization protection. This issue was addressed by unsliding the addresses before returning them.
● CVE-2014-4491 : @PanguTeam, Stefan Esser
Το σχόλιο σας στο forum
You might also like
More from iOS
iOS 13: Dark mode, Nέο Multitasking, Undo/Redo με gestures κ.α.
Το iOS 13 αναμένεται να παρουσιαστεί κατά την έναρξη του WWDC 2019, στις 3 Ιουνίου, ωστόσο δημοσίευμα του 9to5mac μας δίνει από τώρα μία πρώτη γεύση των όσων θα δούμε. iOS 13 - Dark mode Ένα βασικό χαρακτηριστικό της νέας έκδοσης λογισμικού …
iOS 12.2: Τα χαρακτηριστικά και οι βελτιώσεις της νέας έκδοσης λειτουργικού
Το iOS 12.2 είναι διαθέσιμο από εχτές το βράδυ και περιλαμβάνει τέσσερα νέα animoji, καθώς και επιδιορθώσεις σφαλμάτων και βελτιώσεις στο AirPlay, Apple Pay, Safari, Apple Music. Επιπλέον, με τη νέα αναβάθμιση λειτουργικού έρχεται και η υποστήριξη των νέων AirPod …
iOS 12.1.4: Διαθέσιμο το update που διορθώνει το critical bug του FaceTime
Το iOS 12.1.4 περιλαμβάνει σημαντικές ενημερώσεις ασφαλείας, μεταξύ των οποίων και η διόρθωση του critical bug του FaceTime το οποίο επέτρεπε στο χρήστη να ακούει τον παραλήπτη της κλήσης από το μικρόφωνο της συσκευής του προτού ο τελευταίος απαντήσει στην …
iOS 13: Οι πρώτες πληροφορίες για τα χαρακτηριστικά του
Το iOS 13, το επερχόμενο major update του λειτουργικού συστήματος για iPhone/iPad/iPod touch αναμένεται να έρθει με αρκετά νέα χαρακτηριστικά, όπως αναφέρει δημοσίευμα του Bloomberg το οποίο επικαλείται αξιόπιστες πηγές εντός της Apple. Σύμφωνα λοιπόν με τις πρώτες διαρροές, το iOS …
iOS 12.1.3: Τί φέρνει η νέα έκδοση
Το iOS 12.1.3 περιέχει επιδιορθώσεις σφαλμάτων για το iPhone και το iPad, συμπεριλαμβανομένων των εξής: Επιδιόρθωση ζητήματος στα Μηνύματα που μπορούσε να επηρεάσει την κύλιση σε φωτογραφίες στην προβολή «Λεπτομέρειες»Αντιμετώπιση ζητήματος λόγω του οποίου κάποιες φορές οι φωτογραφίες είχαν γραμμωτά τεχνουργήματα …